Shorten URLs via is.gd - free bookmarklet for URL redirection
Friday, May 30, 2008Add this post to Del.icio.us, Digg or Furl | Create Watchlist
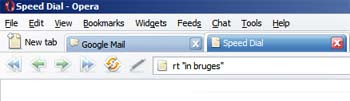
I've started using the free microblogging (or, for me, more microchatting!) service Twitter a lot more lately, but posting URLs (web addresses) within a tweet takes up too much valuable room when you've only got 140 characters to play with.
If you try to include a URL of more than a certain length in a tweet, Twitter does automatically shorten it using TinyURL, but the catch is that the full length of the original longer URL is still counted towards your 140 characters behind the scenes.
So the best course is to reduce or compress the length of the original URL yourself as much as possible first, then paste that "manually" -shortened URL into your tweet.
URL redirection or compression services
There are several free URL redirection services around that will shorten URLs for you, of which I think TinyURL was the first - certainly it's the best known.You feed them your long URL and they produce a reduced short URL you can use instead which, when clicked, will redirect the clicker to the original long URL. Usually you can just copy and paste the tinier URL.
These address compression services are probably most often used to produce short URLs which the user can then paste into an email, as often long URLs which extend over more than one line will "break" in emails and then the recipient won't go anywhere on trying to click them - not unless they edit the URL first, which is problematic for novices who don't realise that, and inconvenient for everyone.
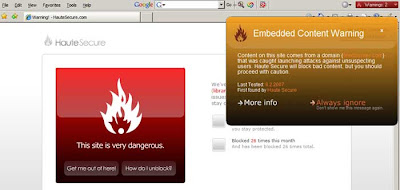
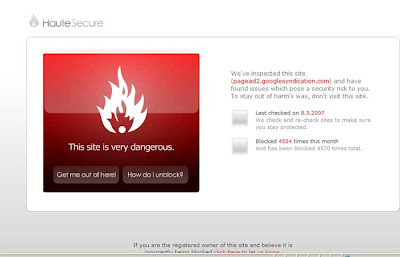
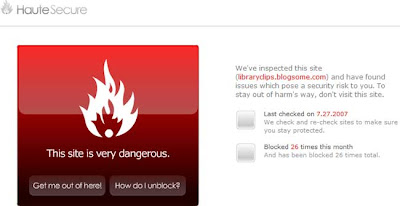
URL redirection services have their risks (see the Wikipedia TinyURL article), of which the main one to me is that the service goes down or goes bust and then their URLs will stop working. But personally I'm willing to take the chance where it's for ephemeral use, e.g. in tweets which people are unlikely to look at after a day or two.
is.gd
 The main service I use for address shortening is is.gd. Why? Because every reduction in character count helps, and is.gd produces the shortest URLs of any URL shortening service I know of: 5 characters in their base URL, compared with 11 in tinyurl.com, for starters. Hey, 6 characters can make all the difference, if like me you find cutting down verbiage hard work!
The main service I use for address shortening is is.gd. Why? Because every reduction in character count helps, and is.gd produces the shortest URLs of any URL shortening service I know of: 5 characters in their base URL, compared with 11 in tinyurl.com, for starters. Hey, 6 characters can make all the difference, if like me you find cutting down verbiage hard work!Also, I like the fact that they produce the shorter URL in a text box, whereas with TinyURL the shortened URL is displayed in the main body of the resulting webpage. Why do I care? Because my Nokia N95 mobile phone lets me copy and paste text (including URLs) from a text box, but not from a webpage - and believe me when you're using a phone without a full keyboard, copy/paste can save bags of time and frustration.
is.gd bookmarklets
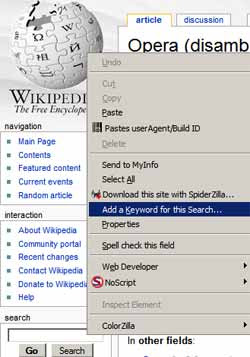
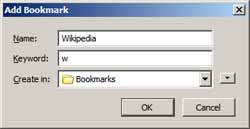
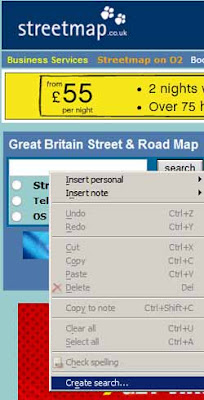
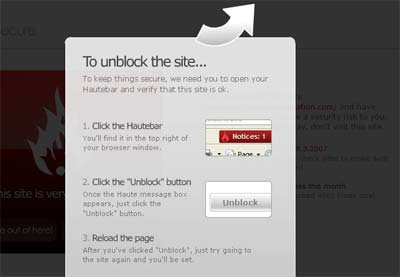
Now is.gd do provide a Shorten with is.gd bookmarklet which you can click in your browser Favorites, Links bar or Bookmarks Toolbar in order to automatically produce their compressed URL for the webpage you're currently visiting (what are bookmarklets / favelets and how to install and use them).But what if you want to shorten a webpage's URL without having to go to that web page first, e.g. you've saved the link to its URL previously or you can just rightclick a link to it to get its URL?
is.gd don't seem to have produced a favelet for that, so I have. Here it is:
is.gd shorten URLs bookmarklet (which I've also added to my page of useful bookmarklets for bloggers)
Hope it's useful!
(For Firefox users there's a much fancier add-on for is.gd you can get, but it's obviously not available for users of other browsers like Internet Explorer, whereas bookmarklets generally work in all sorts of browsers.)
| Links to this post | Post a comment or view 1 comment(s) | Subscribe to all comments on all posts